Code: 04897232
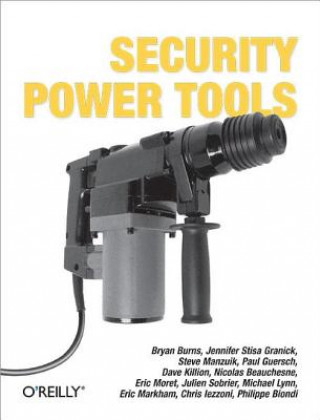
Security Power Tools
by Bryan Burns, Jennifer Stisa Granick, Steve Manzuik, Paul Guersch, Dave Killion, Nicolas Beauchesne, Eric Moret, Julien Sobrier, Michael Lynn, Eric Mar
What if you could sit down with some of the most talented security engineers in the world and ask any network security question you wanted? "Security Power Tools" lets you do exactly that! Members of Juniper Networks' Security Eng ... more
- Language:
 English
English - Binding: Paperback
- Number of pages: 822
Publisher: O'Reilly Media, 2007
- More about this

235.96 zł
RRP: 248.33 zł
You save 12.37 zł

In stock at our supplier
Shipping in 14 - 18 days
You might also like
-
Behold a Pale Horse
105.51 zł -4 % -

Programming in Lua, fourth edition
192.84 zł -

Practical Reverse Engineering: x86, x64, ARM, Windows Kernel, Reversing Tools, and Obfuscation
272.34 zł -
Calligraphy Kit
88.83 zł -11 % -
Puzzle People
130.53 zł -1 % -
Book Of Pf, 3rd Edition
198.87 zł -

Lua 5.2 Reference Manual
50.14 zł -
Z Shell Manual
129.13 zł -
Critical Studies
38.18 zł -23 % -

Comptia Security+
165.11 zł -5 % -
University & College Students
985.26 zł -22 % -

Studying Aging and Social Change
689.80 zł -

Practical JavaScript for the Usable Web
159.08 zł -5 % -

Constructing Test Items
866.57 zł
Give this book as a present today
- Order book and choose Gift Order.
- We will send you book gift voucher at once. You can give it out to anyone.
- Book will be send to donee, nothing more to care about.
More about Security Power Tools
You get 138 loyalty points
 Book synopsis
Book synopsis
What if you could sit down with some of the most talented security engineers in the world and ask any network security question you wanted? "Security Power Tools" lets you do exactly that! Members of Juniper Networks' Security Engineering team and a few guest experts reveal how to use, tweak, and push the most popular network security applications, utilities, and tools available using Windows, Linux, Mac OS X, and Unix platforms. Designed to be browsed, "Security Power Tools" offers you multiple approaches to network security via 23 cross-referenced chapters that review the best security tools on the planet for both black hat techniques and white hat defense tactics. It's a must-have reference for network administrators, engineers and consultants with tips, tricks, and how-to advice for an assortment of freeware and commercial tools, ranging from intermediate level command-line operations to advanced programming of self-hiding exploits." Security Power Tools" details best practices for: reconnaissance - including tools for network scanning such as nmap; vulnerability scanning tools for Windows and Linux; LAN reconnaissance; tools to help with wireless reconnaissance; and custom packet generation; Penetration - such as the Metasploit framework for automated penetration of remote computers; tools to find wireless networks; exploitation framework applications; and tricks and tools to manipulate shellcodes; Control - including the configuration of several tools for use as backdoors; and a review of known rootkits for Windows and Linux.It also details best practices for: Defense - including host-based firewalls; host hardening for Windows and Linux networks; communication security with ssh; email security and anti-malware; and device security testing; Monitoring - such as tools to capture, and analyze packets; network monitoring with Honeyd and snort; and host monitoring of production servers for file changes; Discovery - including The Forensic Toolkit, SysInternals and other popular forensic tools; application fuzzer and fuzzing techniques; and, the art of binary reverse engineering using tools like Interactive Disassembler and Ollydbg. A practical and timely network security ethics chapter written by a Stanford University professor of law completes the suite of topics and makes this book a goldmine of security information. Save yourself a ton of headaches and be prepared for any network security dilemma with "Security Power Tools".
 Book details
Book details
Book category Books in English Computing & information technology Computer networking & communications Network security
235.96 zł
- Full title: Security Power Tools
- Author: Bryan Burns, Jennifer Stisa Granick, Steve Manzuik, Paul Guersch, Dave Killion, Nicolas Beauchesne, Eric Moret, Julien Sobrier, Michael Lynn, Eric Mar
- Language:
 English
English - Binding: Paperback
- Number of pages: 822
- EAN: 9780596009632
- ISBN: 0596009631
- ID: 04897232
- Publisher: O'Reilly Media
- Weight: 1366 g
- Dimensions: 232 × 179 × 49 mm
- Date of publishing: 18. September 2007
Trending among others
-
Web Application Hacker's Handbook: Finding and Exploiting Security Flaws 2e
201.08 zł -10 % -
Ghost in the Wires
93.35 zł -5 % -
Hacker Playbook
121.89 zł -
Nmap Network Scanning
204.80 zł -5 % -
How to Speak Tech
137.17 zł -4 % -
Google Cloud Certified Professional Cloud Network Engineer Guide
243.39 zł -

Blue Team Handbook
88.83 zł -

Wireshark 101
291.33 zł -

GSEC GIAC Security Essentials Certification All-in-One Exam Guide, Second Edition
259.07 zł -5 % -

Wireshark Certified Network Analyst Exam Prep Guide (Second Edition)
226.01 zł -

Stealing the Network: The Complete Series Collector's Edition, Final Chapter, and DVD
366.10 zł -7 % -

Foundations Of Information Security
147.82 zł -14 % -
Python Ethical Hacking from Scratch
211.13 zł -
Countering Cyberterrorism
1035.81 zł -

Metasploit
205 zł -4 % -

Practical Packet Analysis, 3e
201.08 zł -10 % -

UTM Security with Fortinet
307.71 zł -
Practice Of Network Security Monitoring
221.08 zł -23 % -
CISSP Practice Exams, Fifth Edition
120.59 zł -23 % -

Learning Kali Linux
297.96 zł -

PowerShell and Python Together
185.11 zł -5 % -
Tangled Web
238.37 zł -11 % -

Network Security Through Data Analysis
235.96 zł -4 % -
Computer Forensics and Digital Investigation with EnCase Forensic v7
216.66 zł -5 % -
Advanced Persistent Threat Hacking
216.66 zł -5 % -
Cisco ISE for BYOD and Secure Unified Access
329.82 zł -
Cisco ASA for Accidental Administrators
185.11 zł -5 % -
Zero Trust Networks
235.96 zł -4 % -
VMware vSphere Essentials
234.63 zł -

Industrial Network Security
296.76 zł -10 % -

Wireshark Network Analysis (Second Edition)
553.53 zł -

Network Forensics
339.97 zł -

Kali Linux Cookbook
220.58 zł -
Rootkit Arsenal: Escape and Evasion in the Dark Corners of the System
597.20 zł -
Quantum Key Distribution Networks
563.27 zł -

Cisco ASA Configuration
258.97 zł -5 % -

Applied Network Security Monitoring
280.48 zł -
Kali Linux - Assuring Security by Penetration Testing
234.63 zł -

IPv6 Security
315.95 zł -
Wireshark for Security Professionals - Using Wireshark and the Metasploit Framework
216.66 zł -5 % -

Learning Network Forensics
262.32 zł -

Information Assurance Handbook: Effective Computer Security and Risk Management Strategies
258.97 zł -5 % -
Configuring Juniper Networks NetScreen and SSG Firewalls
172.44 zł -20 % -
Dawn of the Code War
85.11 zł -10 % -
Mobile Application Hacker's Handbook
299.67 zł -
IoT Hacker's Handbook
193.34 zł -5 % -

Network Security with OpenSSL
158.87 zł -5 % -
Nmap Essentials
132.20 zł -

Web Application Obfuscation
163.20 zł -19 %
safisfied customers
Since 2008, we have served long line of book lovers, but each of them was always on the first place.
Copyright! ©2008-24 libristo.pl All rights reservedPrivacyPoučení o cookies


 21 million books
21 million books Delivery 12.99 zł
Delivery 12.99 zł (32) 444 93 66 (8-15.30h)
(32) 444 93 66 (8-15.30h)