Kod: 04241595
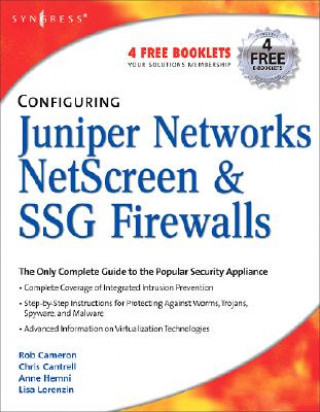
Configuring Juniper Networks NetScreen and SSG Firewalls
Autor Cameron
Juniper Networks Secure Access SSL VPN appliances provide a complete range of remote access appliances for the smallest companies up to the largest service providers. This comprehensive configuration guide will allow system admini ... więcej
- Język:
 Angielski
Angielski - Oprawa: Miękka
- Liczba stron: 768
Wydawca: Syngress Media,U.S., 2006
- Więcej informacji o książce

172.77 zł
Zwykle: 216.03 zł
Oszczędzasz 43.26 zł

Na zamówienie
Wysyłamy za 17 - 26 dni
Zobacz książki o podobnej tematyce
-

Quantum Non-Locality & Relativity - Metaphysical Intimations of Modern Physics 3e
243.65 zł -
Scott Pilgrim's Precious Little Life
48.92 zł -14 % -
Sleepytime Music Book
61.11 zł -23 % -

Game Design Workshop
318.46 zł -

Medallions
100.37 zł -

21st Century Guidebook to Fungi
360.65 zł -
Compact Preliminary for Schools Student's Book without Answers with CD-ROM
75.50 zł -3 % -
Esoteric Tarot
112.56 zł -

American Diner Cookbook
89.90 zł -5 % -

Four Filters Invention of Warren Buffett and Charlie Munger
155.15 zł -
Connemara
51.84 zł -23 % -

Mammalian Synthetic Biology
144.47 zł -

Victorian Afterlives
360.45 zł -

Check Point NGX R65 Security Administration
230.76 zł -9 % -
Open VPN
314.13 zł -
Junos Security
371.62 zł -

Juniper SRX Series
395.99 zł -
Home Art Crochet Book
211.73 zł -

Check Point VPN-1/ FireWall-1 NG Administration
240.23 zł -5 % -

SSL VPN : Understanding, evaluating and planning secure, web-based remote access
262.88 zł -
Juniper Networks Warrior
283.93 zł
Bon podarunkowy: Radość gwarantowana
- Podaruj bon o dowolnej wartości, a my się zajmiemy resztą.
- Bon podarunkowy dotyczy całej naszej oferty.
- Możesz wydrukować elektroniczny bon z e-maila a następnie przekazać go obdarowanemu.
- Ważność bonu wynosi 12 miesięcy od daty wystawienia.
Więcej informacji o Configuring Juniper Networks NetScreen and SSG Firewalls
Za ten zakup dostaniesz 101 punkty
 Opis
Opis
Juniper Networks Secure Access SSL VPN appliances provide a complete range of remote access appliances for the smallest companies up to the largest service providers. This comprehensive configuration guide will allow system administrators and security professionals to configure these appliances to allow remote and mobile access for employees. If you manage and secure a larger enterprise, this book will help you to provide remote and/or extranet access for employees, partners, and customers from a single platform. . Configure Juniper's Instant Virtual Extranet (IVE) Install and set up IVE through either the command line interface (CLI) or Web-based console. . Master the "3 Rs : Realms, Roles, and Resources Realize the potential of the "3Rs for endpoint security, sign-in policies, and authorization of servers. . Get Inside both the Windows and Java Versions of Secure Application Manager (SAM) Learn to implement SAM, manage the end-user experience, and troubleshoot SAM in the field. . Integrate IVE with Terminal Services and Citrix Enable terminal services proxy and configure role options, configure Citrix using a custom ICA, configure terminal services resource policies and profiles, and configure terminal services and Citrix using a hosted Java applet. . Ensure Endpoint Security Use Host Checker, Cache Cleaner, Secure Virtual Workspace, and IVE/IDP integration to secure your network. . Manage the Remote Access Needs of Your Organization Configure Web access, file access and telnet/SSH access for remote users and offices. . Configure Core Networking Components through the System Menu Create clusters, manage virtual systems, and monitor logs, reports, and alerts. . Create Bullet-Proof Sign-in Policies Create standard and custom sign-in pages for both user and administrator access and Secure Meeting pages. . Use the IVE for Log-Related Tasks Perform log filtering, log management, syslog exporting, SNMP management, and system resource monitoring and reporting.
 Szczegóły książki
Szczegóły książki
Kategoria Książki po angielsku Computing & information technology Computer networking & communications Network security
172.77 zł
- Pełny tytuł: Configuring Juniper Networks NetScreen and SSG Firewalls
- Autor: Cameron
- Język:
 Angielski
Angielski - Oprawa: Miękka
- Liczba stron: 768
- EAN: 9781597491181
- ISBN: 1597491187
- ID: 04241595
- Wydawca: Syngress Media,U.S.
- Waga: 1212 g
- Wymiary: 226 × 182 × 55 mm
- Data wydania: 08. December 2006
Ulubione w innej kategorii
-
Web Application Hacker's Handbook: Finding and Exploiting Security Flaws 2e
201.46 zł -10 % -
Ghost in the Wires
93.53 zł -5 % -
Hacker Playbook
122.32 zł -
Nmap Network Scanning
205.39 zł -4 % -
How to Speak Tech
137.63 zł -4 % -
Google Cloud Certified Professional Cloud Network Engineer Guide
243.85 zł -

Blue Team Handbook
89 zł -

Wireshark 101
291.88 zł -

GSEC GIAC Security Essentials Certification All-in-One Exam Guide, Second Edition
259.56 zł -5 % -

Wireshark Certified Network Analyst Exam Prep Guide (Second Edition)
235.09 zł -

Stealing the Network: The Complete Series Collector's Edition, Final Chapter, and DVD
366.69 zł -7 % -

Foundations Of Information Security
148.10 zł -14 % -
Python Ethical Hacking from Scratch
211.53 zł -
Countering Cyberterrorism
1037.36 zł -

Metasploit
183.44 zł -15 % -

Practical Packet Analysis, 3e
201.26 zł -11 % -

UTM Security with Fortinet
308.29 zł -
Practice Of Network Security Monitoring
221.50 zł -23 % -
CISSP Practice Exams, Fifth Edition
120.61 zł -23 % -

Learning Kali Linux
298.52 zł -

PowerShell and Python Together
185.45 zł -5 % -
Tangled Web
238.82 zł -11 % -

Network Security Through Data Analysis
236.40 zł -4 % -
Computer Forensics and Digital Investigation with EnCase Forensic v7
217.07 zł -5 % -
Advanced Persistent Threat Hacking
217.07 zł -5 % -
Cisco ISE for BYOD and Secure Unified Access
330.44 zł -
Cisco ASA for Accidental Administrators
185.45 zł -5 % -
Zero Trust Networks
236.40 zł -4 % -
VMware vSphere Essentials
235.09 zł -

Industrial Network Security
297.32 zł -9 % -

Wireshark Network Analysis (Second Edition)
576.02 zł -

Network Forensics
340.61 zł -

Kali Linux Cookbook
221 zł -
Rootkit Arsenal: Escape and Evasion in the Dark Corners of the System
598.33 zł -
Quantum Key Distribution Networks
564.34 zł -

Cisco ASA Configuration
259.46 zł -5 % -

Applied Network Security Monitoring
281.01 zł -
Kali Linux - Assuring Security by Penetration Testing
235.09 zł -

IPv6 Security
316.55 zł -
Wireshark for Security Professionals - Using Wireshark and the Metasploit Framework
217.07 zł -5 % -

Security Power Tools
236.40 zł -4 % -

Learning Network Forensics
262.88 zł -

Information Assurance Handbook: Effective Computer Security and Risk Management Strategies
259.46 zł -5 % -
Dawn of the Code War
85.27 zł -10 % -
Mobile Application Hacker's Handbook
300.24 zł -

Comptia Security+
165.42 zł -5 % -
IoT Hacker's Handbook
193.71 zł -5 % -

Network Security with OpenSSL
159.17 zł -5 % -
Nmap Essentials
132.49 zł
zadowolonych klientów
Od roku 2008 obsłużyliśmy wielu miłośników książek, ale dla nas każdy był tym wyjątkowym.
Copyright! ©2008-24 libristo.pl Wszelkie prawa zastrzeżonePrywatnieCookies


 21 milionów książek
21 milionów książek Dostawa 10.99 zł
Dostawa 10.99 zł (32) 444 93 66 (8-15.30h)
(32) 444 93 66 (8-15.30h)